Introduction
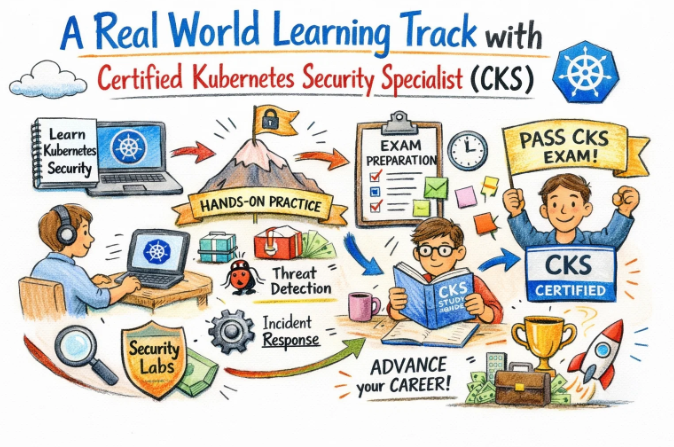
A fundamental shift in how cloud-native environments are managed is being observed across the industry. Security is no longer treated as a final step in the development process. Instead, it is being integrated into every phase of the lifecycle. As Kubernetes continues to be the primary choice for container orchestration, the demand for verified security expertise has grown significantly. The Certified Kubernetes Security Specialist (CKS) is recognized as the essential benchmark for professionals who are tasked with protecting these complex systems. This guide is written to explore the strategic importance of the CKS and how it serves as a cornerstone for secure infrastructure.
The landscape of software delivery has been transformed by automation and cloud technologies. However, this transition has also introduced new types of risks. Vulnerabilities in container images or misconfigured network policies can lead to significant data breaches. To mitigate these threats, a specialized set of skills is required. This guide is intended for those who seek to understand the depth and value of the CKS program.
What is Certified Kubernetes Security Specialist (CKS)?
The CKS is an advanced-level, performance-based certification. It is designed to validate the ability of a professional to secure container-based applications and Kubernetes platforms. The exam is conducted in a live environment where practical security tasks must be completed within a strict timeframe.
Why it matters in today’s software, cloud, and automation ecosystem
In the modern ecosystem, infrastructure is often defined as code. If this code is not secured from the beginning, the entire automation pipeline is compromised. The CKS curriculum focuses on hardening the cluster, securing the supply chain, and monitoring runtime behavior. By achieving this certification, an engineer is prepared to handle the security challenges of highly automated, large-scale systems.
Why certifications are important for engineers and managers
For engineers, a certification provides a structured path for learning complex technologies. It serves as a proof of competence that is recognized globally. For managers, hiring certified professionals is a way to ensure that industry best practices are being followed. It reduces the operational risk and provides a clear framework for team development.
Why Choose DevOpsSchool?
DevOpsSchool is chosen by many because of its deep-rooted connection with the industry. The training is delivered by mentors who have spent years managing production-grade clusters. A heavy emphasis is placed on hands-on labs, ensuring that every concept is understood through practical application. Support is offered throughout the entire certification journey, from initial learning to exam preparation. The curriculum is designed to be beginner-friendly while still providing immense value to experienced professionals.
Certification Deep-Dive: Certified Kubernetes Security Specialist (CKS)
What is this certification?
The CKS is a high-level credential focused on the security of Kubernetes clusters. It tests the practical application of security best practices across the entire container lifecycle.
Who should take this certification?
This program is intended for individuals who already hold the CKA (Certified Kubernetes Administrator) status. It is ideal for System Administrators, Cloud Architects, and Security Engineers who are responsible for maintaining secure environments.
Certification Overview Table
| Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
| DevOps | Advanced | Cloud Engineers | CKA | Supply Chain Security | Post-CKA |
| DevSecOps | Advanced | Security Specialists | CKA | Runtime Monitoring | Post-CKA |
| SRE | Advanced | Reliability Engineers | CKA | Cluster Hardening | Post-CKA |
| AIOps/MLOps | Advanced | AI Infrastructure | CKA | Data Protection | Post-CKA |
| DataOps | Advanced | Data Engineers | CKA | API Security | Post-CKA |
| FinOps | Advanced | Cloud Managers | CKA | Resource Governance | Post-CKA |
Skills you will gain
- System Hardening: Reducing the attack surface of the host operating system.
- Cluster Hardening: Securing the Kube-API server and using RBAC effectively.
- Microservice Security: Using Network Policies to control traffic between pods.
- Supply Chain Security: Implementing image scanning and signing protocols.
- Runtime Security: Detecting threats and anomalies using behavioral analysis.
- Auditing: Configuring and analyzing Kubernetes audit logs.
Real-world projects you should be able to do
- A zero-trust network is implemented within a multi-tenant cluster.
- Vulnerability scanning is integrated into an existing CI/CD pipeline.
- Runtime security alerts are configured to detect unauthorized container access.
- Hardened base images are created and managed across an organization.
- Compliance audits are performed using CIS benchmarks.
Preparation Plan
7–14 Days Plan
- The CKS curriculum is reviewed for all high-level topics.
- Quick labs are performed for Network Policies and RBAC.
- One mock exam is completed to understand the environment.
- The official documentation is bookmarked for quick reference.
30 Days Plan
- Days 1–10: Focus is placed on Cluster and System Hardening.
- Days 11–20: Microservice security and Supply Chain topics are covered.
- Days 21–30: Intensive practice with runtime tools and mock tests is conducted.
60 Days Plan
- Month 1: Every domain is studied in detail. Deep dives into tools like Falco and Trivy are completed.
- Month 2: Scenario-based troubleshooting is practiced. Speed is improved by repeating complex tasks in a terminal.
Common mistakes to avoid
- The CKA certification is allowed to expire before taking the CKS.
- The importance of speed in the terminal is underestimated.
- Generic YAML files are used without checking the specific cluster context.
- The official documentation is not used effectively during practice.
- Theoretical knowledge is prioritized over hands-on lab work.
Best next certification after this
- Same Track: Certified Kubernetes Application Developer (CKAD).
- Cross-Track: AWS Certified Security – Specialty.
- Leadership / Management: Certified Information Security Manager (CISM).
Choose Your Learning Path
1. DevOps Path
The automation of security checks is the focus here. This path is for those who build the infrastructure and want to ensure it is secure from the moment it is created.
2. DevSecOps Path
Security is treated as a continuous process. This path is designed for professionals who want to bridge the gap between traditional security and modern DevOps.
3. Site Reliability Engineering (SRE) Path
System uptime is protected by preventing security-related incidents. This path emphasizes auditing and the use of runtime security to maintain reliability.
4. AIOps / MLOps Path
Large-scale data processing clusters are secured. This path is best for those managing the infrastructure used for artificial intelligence and machine learning.
5. DataOps Path
Data integrity and privacy are maintained throughout the pipeline. This path focuses on securing access to sensitive data stored within Kubernetes.
6. FinOps Path
Governance is applied to manage cloud costs and security simultaneously. This path is for those who oversee the financial and operational health of the cloud.
Role → Recommended Certifications Mapping
| Role | Same-Track Recommendation | Cross-Track Recommendation | Leadership Focus |
| DevOps Engineer | CKS | Terraform Associate | PMP |
| SRE | CKS | Prometheus Certified | ITIL v4 |
| Platform Engineer | CKS | CKA | Certified Cloud Manager |
| Cloud Engineer | CKS | AWS Solutions Architect | MBA (IT) |
| Security Engineer | CKS | Certified Ethical Hacker | CISM |
| Data Engineer | CKS | Google Data Engineer | Data Governance |
| FinOps Practitioner | CKS | FinOps Certified | Finance for Managers |
| Engineering Manager | CKS | Agile Leader | CTO Program |
Next Certifications to Take
For the Technical Professional:
- Same-track: Certified Kubernetes Administrator (CKA).
- Cross-track: HashiCorp Certified: Terraform Associate.
- Leadership: Certified Scrum Master (CSM).
For the Security Specialist:
- Same-track: Offensive Security Certified Professional (OSCP).
- Cross-track: Google Professional Cloud Security Engineer.
- Leadership: CISO Certification.
Training & Certification Support Institutions
DevOpsSchool
Training for modern IT roles is delivered here. A practical approach is maintained to ensure that every student is ready for the industry.
Cotocus
Professional consulting and technical education services are offered. The focus is on high-level technologies and enterprise-grade solutions.
ScmGalaxy
A wide range of resources for software configuration and DevOps is provided. Technical blogs and community support are key features of this institution.
BestDevOps
Practical training programs are designed for engineers seeking career growth. Job-oriented skills and certification success are prioritized.
devsecopsschool.com
Specialized training in security-integrated development is provided. It helps professionals master the intersection of security and DevOps.
sreschool.com
Education on system reliability and scalability is offered. It prepares engineers to manage and secure high-availability production environments.
aiopsschool.com
The intersection of AI and IT operations is explored here. Training is provided to manage the next generation of automated systems.
dataopsschool.com
The discipline of managing data lifecycles with a DevOps mindset is taught. It focuses on secure and efficient data engineering.
finopsschool.com
Cloud financial management and governance are taught here. It helps teams balance cost, speed, and security in the cloud.
FAQs Section
- Is the CKS exam purely theoretical?
No, it is a completely practical, performance-based exam conducted in a live terminal. - How long should one study if they already have CKA?
A period of 4 to 8 weeks is usually recommended for most professionals. - Can the exam be taken from home?
Yes, the exam is proctored remotely and can be taken from a quiet location with a good internet connection. - What happens if the exam environment is slow?
The proctor should be notified immediately, and standard troubleshooting steps are usually followed. - Is CKS relevant for local Indian companies?
Yes, many Indian tech firms and global captives are now making CKS a mandatory requirement for senior roles. - Does CKS cover cloud provider security?
It focuses on Kubernetes-native security, which is applicable to all cloud platforms. - What is the best way to remember command-line flags?
Frequent practice and the use of the official documentation during labs are highly suggested. - Are third-party security tools tested in CKS?
Yes, tools such as Falco and image scanners are included in the exam syllabus. - Can the certification be renewed?
The certification is valid for two years, after which the exam must be taken again. - Is there a community for CKS aspirants?
Many online forums and groups, such as those hosted by ScmGalaxy, provide excellent peer support. - How much does the exam cost?
The official price is set by the Linux Foundation, though discounts are often available through training partners. - Are Linux skills required for CKS?
A strong understanding of Linux fundamentals is essential for system hardening tasks.
Certified Kubernetes Security Specialist (CKS) Specific FAQs
- Is image signing covered in the exam?
Yes, the ability to implement and verify signed images is a key part of the supply chain security domain. - How is runtime security tested?
Tasks often involve configuring Falco rules or inspecting logs to identify suspicious activity. - What is the weightage of Network Policies?
Network security is a high-priority area and usually accounts for a significant portion of the total score. - Are specific API server flags tested?
Yes, the knowledge of hardening the API server through various flags is frequently evaluated. - Is the use of an IDE allowed?
No, the exam is conducted in a basic terminal environment using editors like Vim or Nano. - Can documentation from GitHub be used?
Only specific official Kubernetes and tool documentation sites are allowed during the test. - What is the passing score for the CKS?
A minimum score of 67% is required to be awarded the certification. - How are the clusters provided in the exam?
Several different clusters are usually provided, and the correct context must be selected for each task.
Testimonials
Arjun
A deep understanding of how to protect clusters was developed through this training. The focus on hands-on labs was exactly what was needed for the exam.
Kavita
The transition to a security-focused role was made much easier. The concepts were explained in a very simple and practical way.
Liam
My confidence in handling production-level security audits has grown significantly. The mentorship provided was grounded and very helpful.
Mei
The strategic importance of the CKS was clearly highlighted. It is a must-have for anyone serious about cloud-native infrastructure.
Omar
The practical scenarios provided during the training were very similar to real-world challenges. A clear path for career growth was established.
Conclusion
The Certified Kubernetes Security Specialist (CKS) is an invaluable asset in the modern cloud-native era. It ensures that the highest level of security is maintained across the entire software delivery lifecycle. The long-term career benefits are immense, offering both recognition and the ability to lead complex security projects. Strategic planning and a commitment to continuous learning are encouraged for all professionals who wish to excel in this field.